Bill Mill
(replying to Julia Evans)
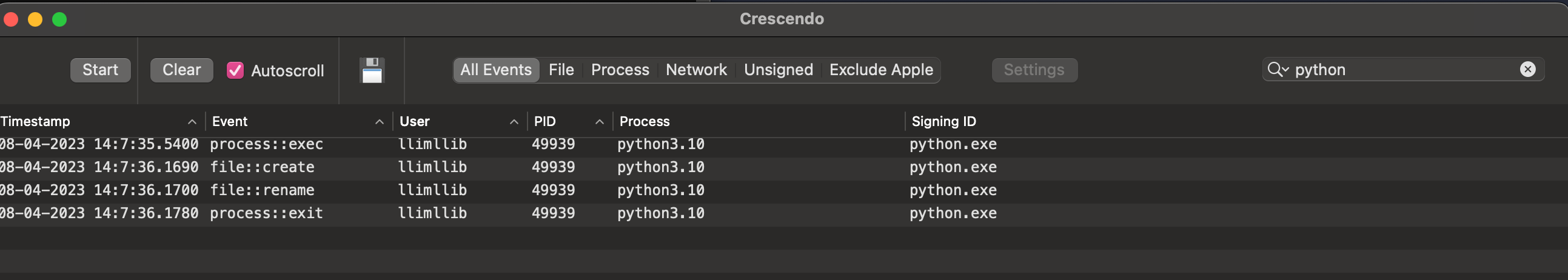
@b0rk The closest I know how to get on a mac without disabling SIP is to install an app that uses a kernel extension to monitor system events. Here's crescendo (https://github.com/SuprHackerSteve/Crescendo) for example:
Bill Mill
(replying to Bill Mill)
@b0rk it will show you file creation and removal, but not stat unfortunately
Bill Mill
(replying to Bill Mill)
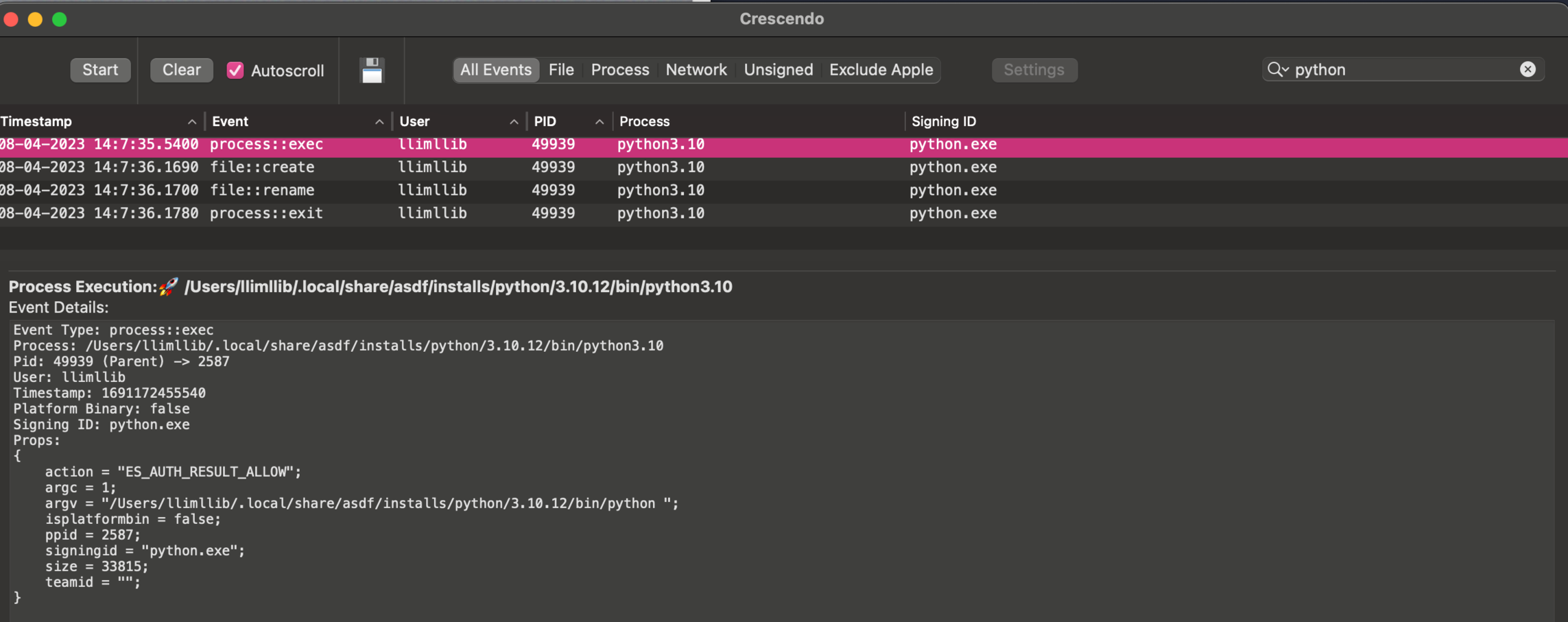
@b0rk oh I should have included that it gives you details on the events too, here's the python exec:
Bill Mill
(replying to Bill Mill)
@b0rk If you disable SIP, you can use dtrace or dtruss like strace I think, I'm just not willing to do that to test it out at the moment - if you're interested I can dig into it ab it
Bill Mill
(replying to Bill Mill)
@b0rk process monitor and file monitor appear to do the same thing with the same os tools on the command line, but I haven't tried them out: https://objective-see.org/products/utilities.html#FileMonitor